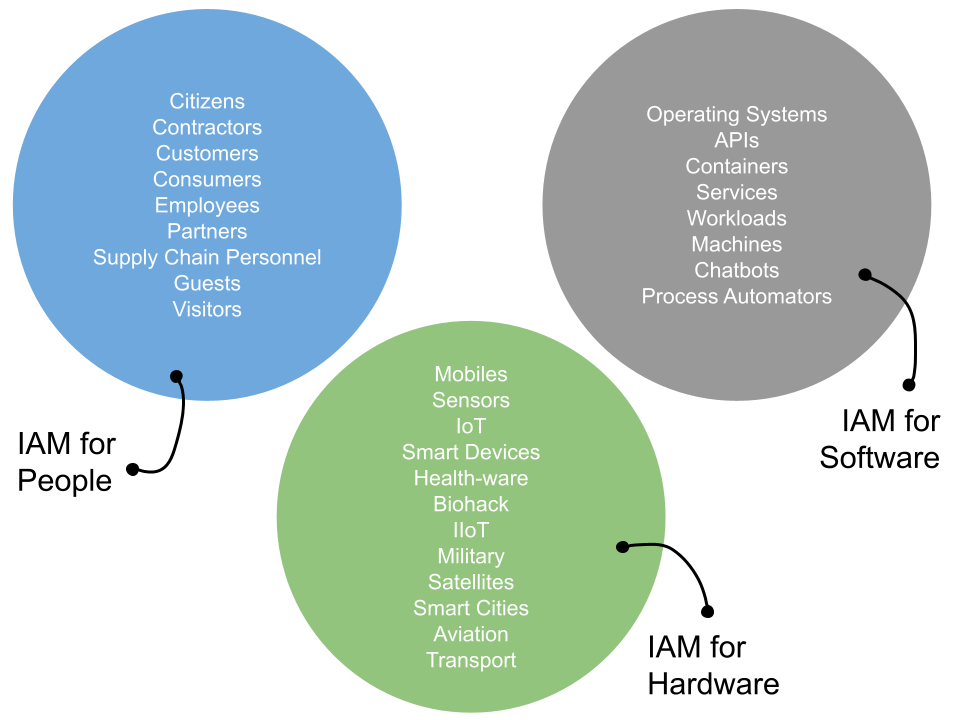
A discussion on the need to consider identity management as a set of life cycles - for expansion into the workload and NHI spaces.
Join our founder Simon Moffatt in our next industry webinar, where he will be in conversation with cloud identity governance and administration provider Omada on the concept of cloud IGA.
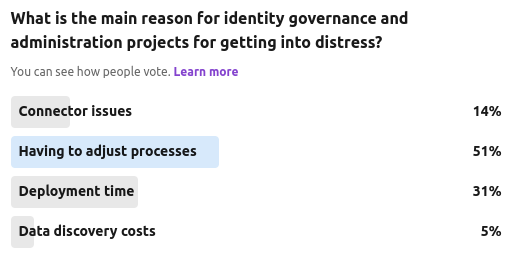
Identity Governance and Administration is now entering a new age – where the IGA problem statement has evolved, the opportunity to innovate and improve productivity are all around, yet many organizations are struggling with fragile and static on-premises IGA technologies built for yesterday’s problems.
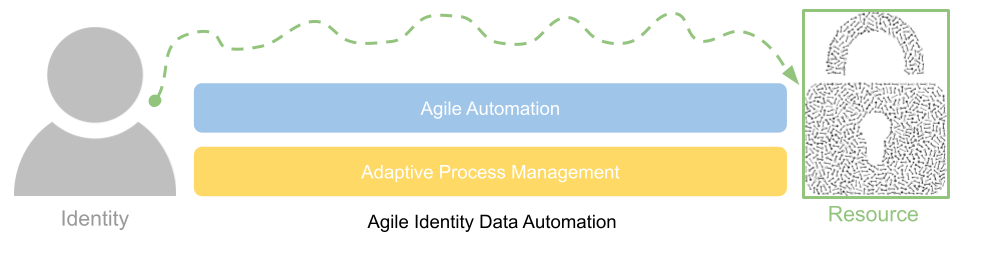
A discussion on why existing IGA projects are often in distress and how a more agile data automation approach can streamline process and improve application connectivity.
Next week our founder Simon Moffatt will be speaking at event in London with leading customer identity and access management platform provider Transmit Security.
The event is entitled "The Fusion of Identity Management and Fraud Prevention" and will take place on May 23rd at One Great George Street London. The day long gathering will contain an array of guest talks from industry leaders, practitioners and consultants, discussing the rise of fraud within the identity life cycle - from account on-boarding and proofing through to deepfake authentication techniques.
Join us for our next free industry webinar in April: The Evolution of Authorization: How To Achieve Zero Standing Privileges.
Organisations are struggling to deliver applications and services on time, often due to hard coded permissions and access control components. Coupled with that, emerging threats and a lack of dynamic and contextual policy controls are increasing risk to key data assets.
Our founder Simon Moffatt will be attending RSA Conference 2024 in San Francisco in early May. He will be available for vendor briefings, after-event functions and vendor support.
To arrange a meeting, please contact us.
A discussion on modern identity governance and administration requirements and why many projects are in distress.
Our latest community poll was focused on the ever growing murmur that many privileged access management (PAM) and identity governance and administration (IGA) capabilities are either starting to overlap, or dedicated solution providers from each world are starting to add in "lite" functions from each others feature set.
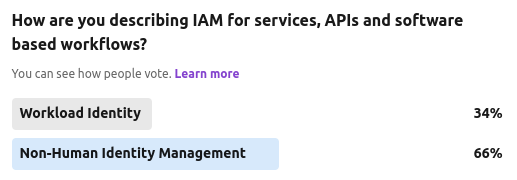
We ran another anecdotal community poll recently, asking whether this area of service IAM should be termed as "workload identity" or the more emerging "non-human identity".
The Cyber Hut recently ran a 7 day community poll on LinkedIn asking which of four big-ticket items will organisations be looking at from an identity and access management point of view.