A discussion on the need to consider identity management as a set of life cycles - for expansion into the workload and NHI spaces.
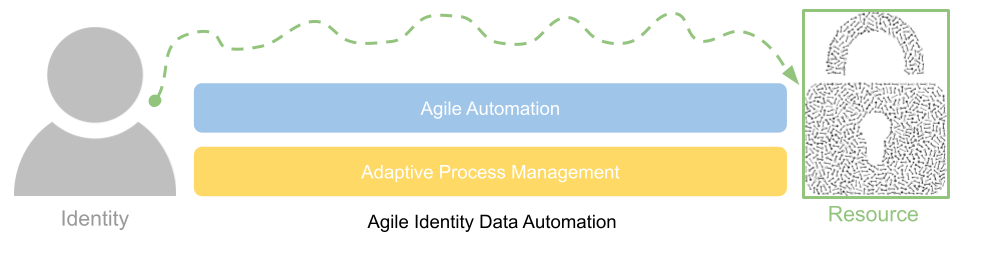
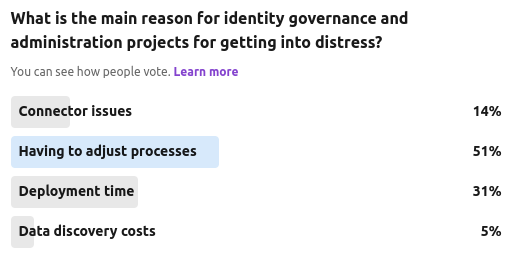
A discussion on why existing IGA projects are often in distress and how a more agile data automation approach can streamline process and improve application connectivity.
A discussion on modern identity governance and administration requirements and why many projects are in distress.
Our latest community poll was focused on the ever growing murmur that many privileged access management (PAM) and identity governance and administration (IGA) capabilities are either starting to overlap, or dedicated solution providers from each world are starting to add in "lite" functions from each others feature set.
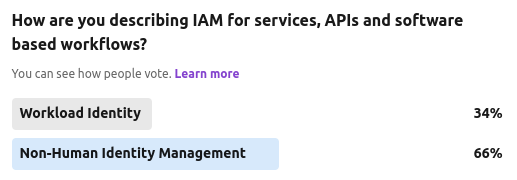
We ran another anecdotal community poll recently, asking whether this area of service IAM should be termed as "workload identity" or the more emerging "non-human identity".
The Cyber Hut recently ran a 7 day community poll on LinkedIn asking which of four big-ticket items will organisations be looking at from an identity and access management point of view.
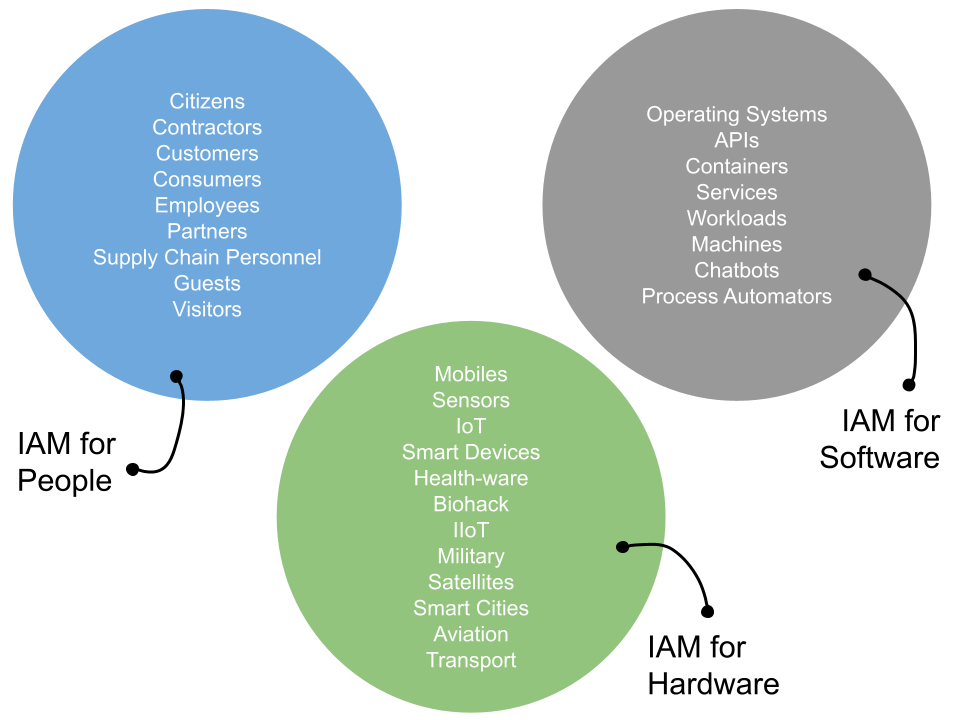
So in this respect how does a workload differ from a machine? Well machines will typically be host centric and operating system related. That could be anything from bare metal servers (remember those?) right through to more specific devices working in the IoT, industrial IoT, aviation, transport or medical spaces....
This four-day security extravaganza tours the world, and I attended the keynotes and briefings sessions on the 6th and 7th. Clearly this is a broader security conference, but as always the role of identity and access management appears in more ways than previous and often in slightly less obvious ways.
Machines are eating the world. Or is it software? No wait, it's AI. In someways, it will likely be none, neither or all. I don't think any will make us all extinct, yet automation, the use of machines and services (powered by clever software) will certainly be doing more for us as humans than ever before - as employees, customers and citizens.
In light of the recent integration of ForgeRock into Ping Identity, The Cyber Hut has received numerous inquiry calls regarding potential integrations, feature overlap, next steps and existing deployment advice. To that end, we're making available a basic feature comparison matrix that highlights the basic capabilities each vendor as in each of the main identity areas of B2E and B2C. This matrix was compiled using publicly available references with peer review by those who have implemented ForgeRock or Ping technologies in the last 3 years.