In light of the recent integration of ForgeRock into Ping Identity, The Cyber Hut has received numerous inquiry calls regarding potential integrations, feature overlap, next steps and existing deployment advice. To that end, we're making available a basic feature comparison matrix that highlights the basic capabilities each vendor as in each of the main identity areas of B2E and B2C. This matrix was compiled using publicly available references with peer review by those who have implemented ForgeRock or Ping technologies in the last 3 years.
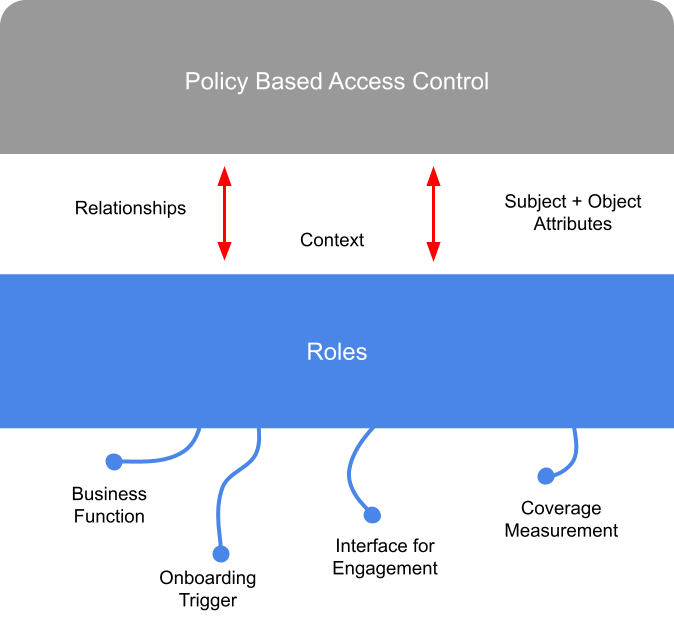
A discussion on how role based access control may still deliver business value, if deployed in a slightly different way.
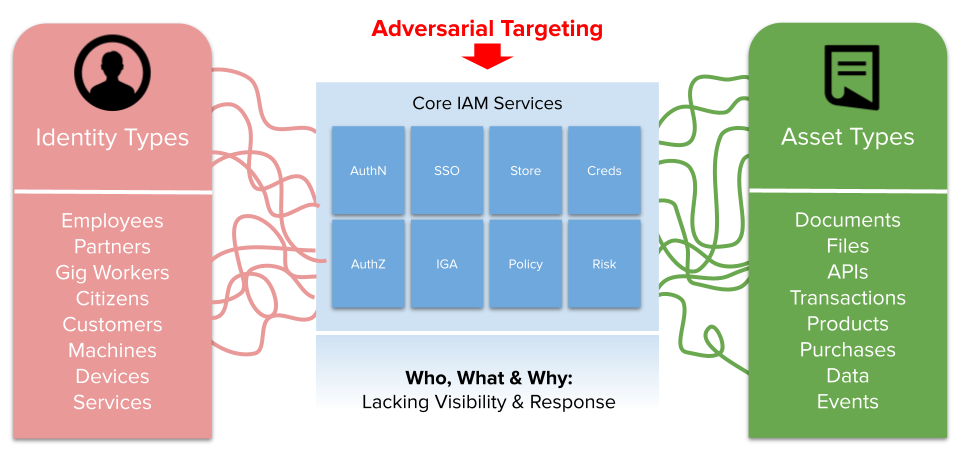
I wanted to expand to this based on conversations I've had over past 4-5 months as part of a research report coming out soon from The Cyber Hut on ITDR - what it is and why it's important now. The last thing I want to do however, is create more confusion and definitions! In order to avoid that I want to break down the term bit by bit.
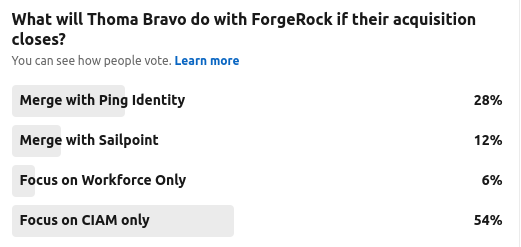
An opinion piece analysing the potential acquisition of ForgeRock by private equity firm Thoma Bravo.
I wanted to wrap up 2022, with an anecdotal look at some of the key facts and figures that made up the bulk of The Cyber Hut's interactions, research and community engagement over the past year.
It has been a great year professionally and personally, yet parts of the world are still being ravaged by the pandemic, conflict, economic turmoil and the cost of living crisis. Hopefully 2023 can start to stabilise some of those broader problems we will undoubtedly all feel in the coming months.
I want to take a retrospective look back at 2022 in numbers, adding in a few stories and comments as I go. I hope you enjoy it and thank you to all of the global identity and access management community who have engaged with The Cyber Hut over the past 12 months.
The next NIS-D directive is live in a second iteration and regulators of Critical National Infrastructure (CNI) across Europe are working to evaluate and adapt the directive to country specific regulations. Thus, the UK (through the Department of Culture Media & Sport) have issued their consultation outcome for regulation of managed service providers and updates to the NIS regulation.
Zero Trust has been with us for the best part of a decade - since the likes of the Jericho Forum, Google's Beyond Corp and ex-Forrester analyst John Kindervag have all promoted a view of moving the concept of "trust" from a location to a concept based on the identity, device and associated context.
Version 2.0 of the US Department of Defence Zero Trust Reference Architecture has been cleared for public release and is a good, detailed read regarding an actual migration and implementation model. The document is available here.
This week saw the FIDO Authenticate conference take place in Seatle. I attended via the virtual remote route, going through the vast majority of the sessions from the comfort of the office. A few items that stood out for me.
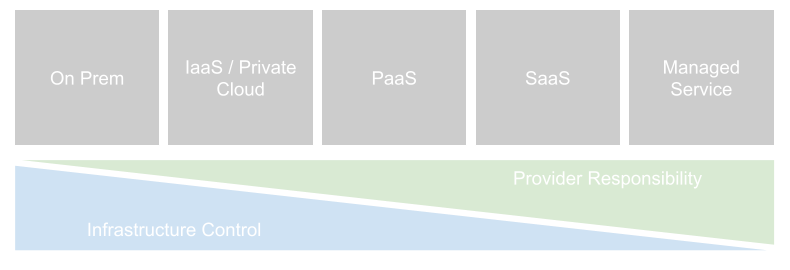
Even as many organisations are moving to a "cloud first" strategy for the consumption of new applications and services, the cloud line is blurred. Not all services can be consumed in a pure cloud setting, and not all "clouds" are the same.
Any analysis in the popularity, options or strategy with respect to IAM deployment should be firmly based against a set of basic definitions.