Machines are eating the world. Or is it software? No wait, it's AI. In someways, it will likely be none, neither or all. I don't think any will make us all extinct, yet automation, the use of machines and services (powered by clever software) will certainly be doing more for us as humans than ever before - as employees, customers and citizens.
Our founder Simon Moffatt will be speaking at FIDO Authenticate 2023 in Carlsbad San Diego October 16-18th.
This three-day auth-fest will see the world's authentication, authorization and identity experts converge for some deep dive discussions and networking on a broad array of topics - from passkeys and biometrics, through to proofing and access control.
In light of the recent integration of ForgeRock into Ping Identity, The Cyber Hut has received numerous inquiry calls regarding potential integrations, feature overlap, next steps and existing deployment advice. To that end, we're making available a basic feature comparison matrix that highlights the basic capabilities each vendor as in each of the main identity areas of B2E and B2C. This matrix was compiled using publicly available references with peer review by those who have implemented ForgeRock or Ping technologies in the last 3 years.
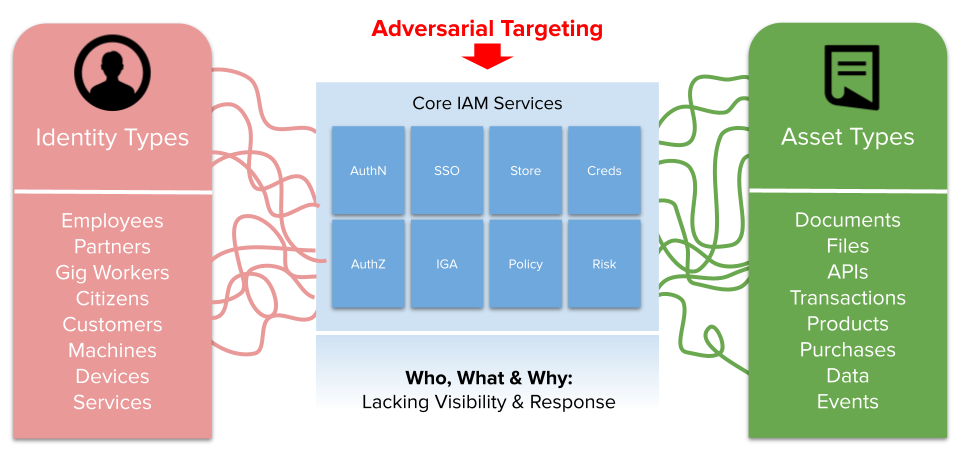
Join us on Sept 27th for our latest industry webinar. We will be launching our latest industry report on Identity Threat Detection and Response, as well as hosting an industry panel of global identity and access management experts and leaders, to discuss the threats to our critical IAM infrastructure.
MANCHESTER, UNITED KINGDOM, August 22, 2023 — The Cyber Hut, a leading boutique industry analyst and […]
Join us on August 22nd at 4pm UK time for our latest industry webinar where our founder Simon Moffatt will be in conversation with Alex Bovee - CEO at ConductorOne, a leader in identity centric security.
Identity Governance and Administration has been with us over 2 decades - yet the problem statement it tries to solve gets larger and the solution set continues to innovate.
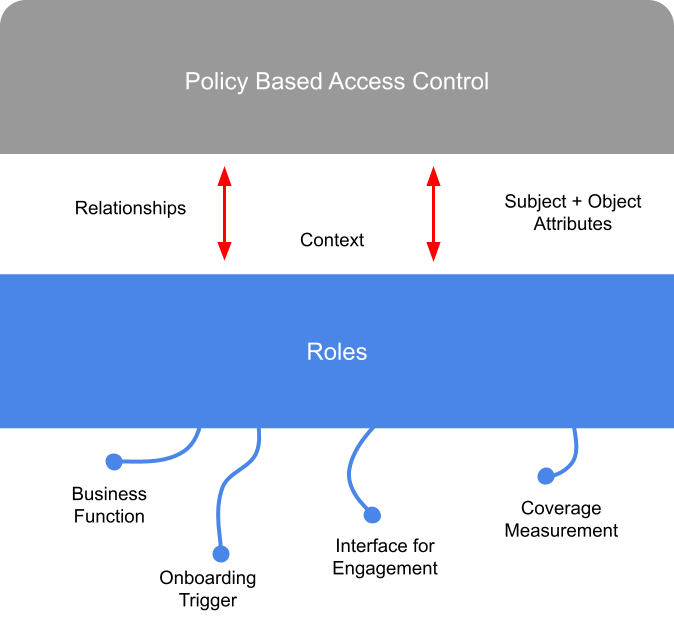
A discussion on how role based access control may still deliver business value, if deployed in a slightly different way.
I wanted to expand to this based on conversations I've had over past 4-5 months as part of a research report coming out soon from The Cyber Hut on ITDR - what it is and why it's important now. The last thing I want to do however, is create more confusion and definitions! In order to avoid that I want to break down the term bit by bit.
Next week our founder Simon Moffatt will be in conversation with Mattia Zago from Monokee, where they'll be discussing the evolution of identity and access management platforms to include key visualisation and orchestration capabilities.
Our founder Simon Moffatt will be delivering a keynote presentation at the Heliview Identity and Access […]