Join us for our next free industry webinar in April: The Evolution of Authorization: How To Achieve Zero Standing Privileges.
Organisations are struggling to deliver applications and services on time, often due to hard coded permissions and access control components. Coupled with that, emerging threats and a lack of dynamic and contextual policy controls are increasing risk to key data assets.
Our founder Simon Moffatt will be attending RSA Conference 2024 in San Francisco in early May. He will be available for vendor briefings, after-event functions and vendor support.
To arrange a meeting, please contact us.
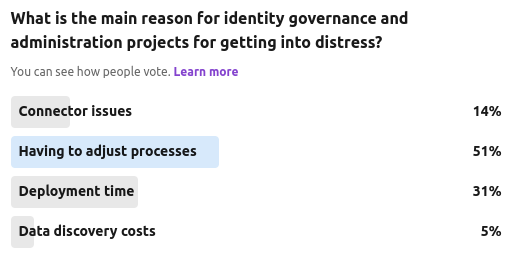
A discussion on modern identity governance and administration requirements and why many projects are in distress.
Our latest community poll was focused on the ever growing murmur that many privileged access management (PAM) and identity governance and administration (IGA) capabilities are either starting to overlap, or dedicated solution providers from each world are starting to add in "lite" functions from each others feature set.
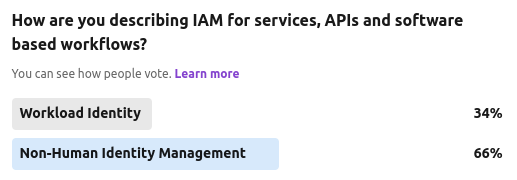
We ran another anecdotal community poll recently, asking whether this area of service IAM should be termed as "workload identity" or the more emerging "non-human identity".
The Cyber Hut recently ran a 7 day community poll on LinkedIn asking which of four big-ticket items will organisations be looking at from an identity and access management point of view.
So in this respect how does a workload differ from a machine? Well machines will typically be host centric and operating system related. That could be anything from bare metal servers (remember those?) right through to more specific devices working in the IoT, industrial IoT, aviation, transport or medical spaces....
This four-day security extravaganza tours the world, and I attended the keynotes and briefings sessions on the 6th and 7th. Clearly this is a broader security conference, but as always the role of identity and access management appears in more ways than previous and often in slightly less obvious ways.
Next week the Chartered Institute of Information Security live event comes to Manchester - and home of Manchester City football club at the Etihad Stadium.
This full day event will bring together cyber security leaders and experts from across the UK, for a day of presentations, panels, case studies and vendor interaction.
This week our founder Simon Moffatt will be presenting at a C-level round table being held […]