Microsoft have been in the identity and access management space for over 20 years – since the success of their first directory services product integrated into Windows Server 2000. You could argue the Windows NT ecosystem prior to that was really their first identity related foray with the NTUSER.DAT file system. But let’s not go there.
Are They an Identity Player?
Interestingly in recent times, Microsoft wouldn’t probably describe themselves as an identity and access management specialist player. Their latest SEC 10K annual filing uses the word “identity” 11 times – in the context of their four pillars being “security”, “compliance”, “identity” and “management” (interestingly the word identity doesn’t appear at all in the Google or Amazon latest filings…). As such many think of Microsoft of a productivity provider (O365), gaming, infrastructure and lately with more specialised search, AI and decentralised capabilities.
Enter Entra Stage Left
A couple of things to consider. They recently re-branded their identity capabilities Entra. Not quite sure what that stands for, but it’s good for SEO undoubtedly. Back in 2021 they acquired cloud infrastructure entitlements management (CIEM) provider Cloudknox. Microsoft also provide a decent set of identity related services covering the usual b2e and b2c directory via Azure as well as some interesting forays into decentralised IAM and then the CIEM related acquisition. Their IoT and machine to machine approach seems lacking maturity, but as do all but the most specialist of vendors anyway in these areas.
The main Entra strap line is “Secure Access for Connected World”. Generic enough to allow expansion via organic development, or perhaps more naturally via partnerships and in turn acquisitions.
Identity Governance
From an identity governance perspective this is clearly very focused on Azure AD – with some workflow integrations for HR for the b2e world. There are some existing connectors for things like Success Factors and Workday. Downstream cloud connectivity comes in the form of a cloud connector service. A common use case is going to be on-prem AD syncing to Azure AD which the documentation provides solid coverage for. The access review documentation seems a little weak and the role based features also quite basic.
Verified ID
Their Verified ID capabilities seem focused on strong identity proofing during enrolment. This seems focused at the workforce more than consumer – with remote employee on-boarding seeing a huge spike in demand since the pandemic.
Permissions Management
The Cloudknox acquisition is re-branded Permissions Management. This model typically follows a discover, remediate and monitor process. This utilises a Linux box which gets deployed into the cloud infrastructure that needs monitoring – clearly the interesting angle being this doesn’t need to be Microsoft’s.
Azure AD – B2E and B2C
Azure AD capabilities have grown beyond standard user profile storage to include adaptive access, identity protection and seamless experiences aimed at reducing the reliance on help desk interaction.
The Azure AD for External Identities is essentially the re-brand for consumer or customer identity projects. The first 50,000 monthly active users are free – which could be quite compelling for an organisation already using Microsoft technologies elsewhere.
Workload Identity
Microsoft have also provided a preview for something they term Workload Identity. This is focused on machine to machine identity, and the growing need for non-person entity services. This seems quite early in the maturity curve for them, but it is certainly something to watch.
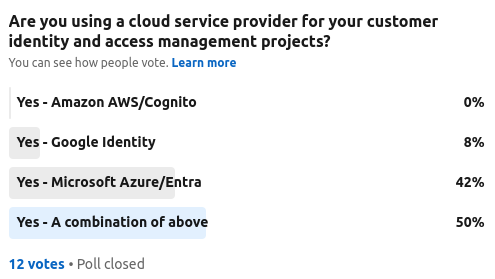
An interesting aside, The Cyber Hut ran two polls recently, asking the community whether Microsoft was being chosen (along with AWS or Google) for both consumer and workforce identity. The results were quite interesting:
From a consumer perspective, the response was low – indicating that none of the big three cloud service providers were being used by the respondents.
From a workforce b2e point of view, the numbers where higher – which is not surprising due to the maturity in the b2e market compared to consumer and also compared to the maturity of Microsoft’s offerings in the workforce space.
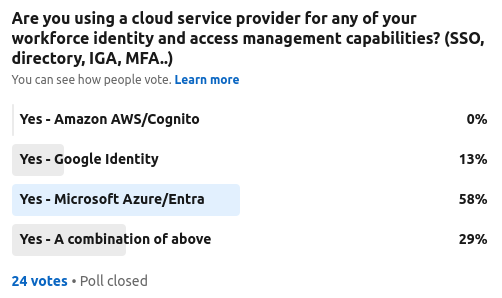
Either way, it seems Microsoft is at least leading the IAM charge perhaps from the other CSP’s. Time will tell whether they continue to invest to start actively competing with more specialist providers such as Okta, Ping Identity, ForgeRock et al.
