Last week I had the pleasure of presenting a rapid and remote 10 minute keynote at the southern LATAM IAM Tech Day Event.
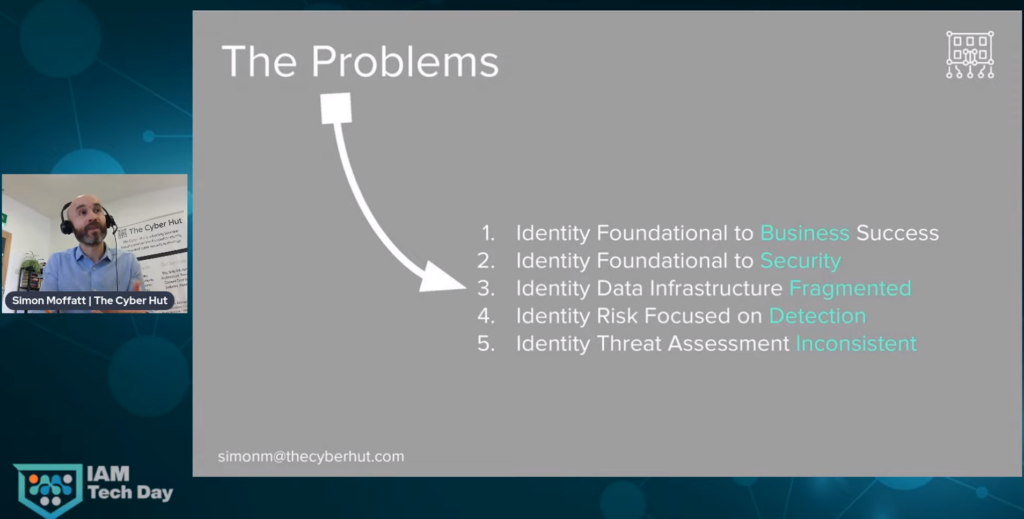
I chose to introduce a topic that has been emerging over the past 12 months – an assessment framework specifically focused on identity and access management risk across the enterprise. Identities now come in four main pillars – typically employees, consumers (or customers), IoT and devices as well as machines and APIs.
Why do we need this? Well I have been involved in numerous buy-side industry workshops and advisory sessions over the past year, where identity threat has been tackled on some specific life cycles. Typically things like consumer authentication – and how to design those end user journeys from cradle to grave, where risk is identified and treated – through to analysing and understanding the identity and access management threat surface for the IoT landscape.
In all these different cases, a model starts to emerge – where firstly the identity assets need to be identified. This seems simple, but is often not always completed. What assets are we referring to? Well clearly identity repositories, permissions databases, the personas involved, devices involved and of course the assets being accessed and the contextual signalling needed to analyse those access control decisions.
Secondly it seems important to be able to glue those assets together – so what exactly is the identity trying to achieve? This is essentially the W5 access path – the who, what, where, why and what.
This platform then allows us to apply some baseline identity controls – controls which are quite well known and available from numerous existing repositories such as Mitre, OWASP, ISO27002, NIST RMF or the Center for Internet Security.
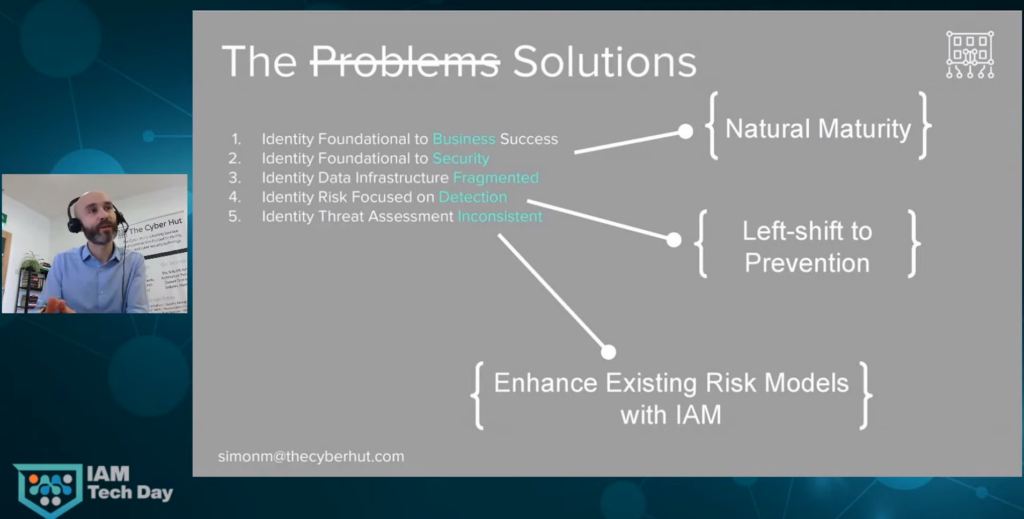
Clearly not all controls need applying – and more importantly it is important to then have a system of risk management (assessment and treatment) in place to handle exceptions. So what does that mean? Well what happens if you identify 15% dormant accounts in a corporate directory? Or find that in a consumer identity system, the number of credential resets peaks during particular times of the month from particular locations? A standard and repeatable approach that results in controls coverage reporting and assurance helps organisations understand how to treat and how to report against those control exceptions.

Watch the key note here.
