The last 6 months has seen some interesting innovation occur within the privacy and data security spaces. It seems some specific decoupling of end to end encryption, privacy vaulting and data centric security is starting to occur.
Why is this interesting? Typically organisations have tackled the privacy situation using two pretty large tools: data storage encryption and encryption of data in flight – namely, applying TLS to all connections – both within controlled and uncontrolled areas.
Skyflow is perhaps offering something different.
Keyfacts
| Website | https://www.skyflow.com/ |
| Locations | Palo Alto, CA, USA; Bangalore, India |
| CEO | Anshu Sharma (LinkedIn, Twitter), ex Salesforce, Oracle |
| CTO | Prakash Khot (LinkedIn, Twitter), ex Salesforce, CA |
| Number of employees | <40 |
| Founded | 2019 |
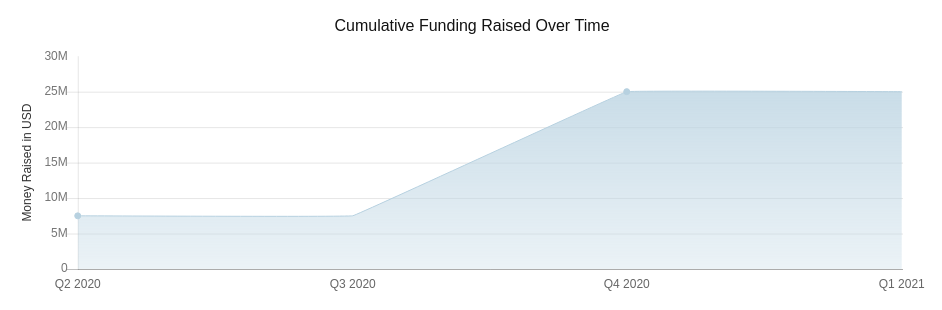
Funding
Skyflow has had two rounds of venture funding – a seed round of $7.5 million in May 2020, lead by Foundation Capital. This was followed up in December 2020 with another $17.5 million in a series A round. This was lead again by Foundation along with Canvas Ventures.
Value Proposition
Skyflow is attacking the privacy space. Their blog material over the past 12 months has seen them focus upon the concept of delivering privacy via an API-first approach, backed by a data privacy vault. Many applications either single page apps, or mobile apps will be handling sensitive data – like PII for example.
Skyflow aims to allow application developers to have simple and rapid access to privacy preservation technologies, without having to be experts in privacy technology. They position their technology to provide a faster time to market for developers – privacy and security shouldn’t slow down the application go to market.
It seems their main customer target verticals, would be health-tech and fin-tech – both of which handle sensitive data, whilst also face significant market change, challenge and transformation.
Their main adoption persona seems to be that of developers – according to their launch blog in Dec 2020, which indicated they had spent 2 years in stealth building up their product set after interviewing and working with the developer community and how they handled data security.
Technical Introduction
Some basics straight from the Skyflow docs. Skyflow is a service offering (sitting on to of AWS with a 99.9% uptime), focused on delivering a data vault where sensitive data can be stored. The vault can be accessed by a REST API to create and read data blocks.
A vault is essentially a secure database, backed by a schema – Skyflow provide some template schemas to accelerate the getting started process.
That REST API seems to be accessible via the creation of service accounts, that link your application to the underlying vault. The service account relies on bearer tokens as a means of authentication. That bearer token is created on the back of a JWT token presentation. So essentially JWT token authentication.
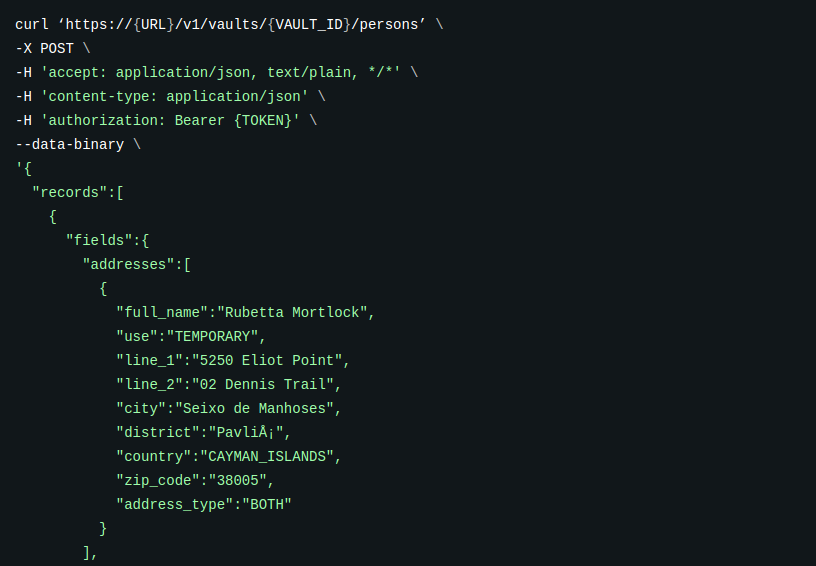
Skyflow Vault
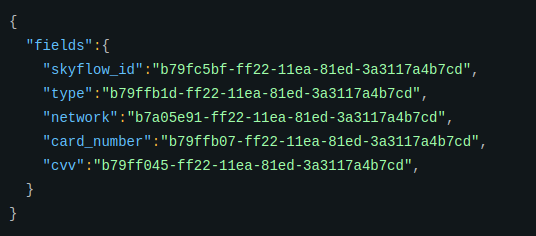
Data is created in the vault over the REST API, allowing pretty simple and rapid integration. The data creation process will bounce back a record Id which can then be used for future data queries.
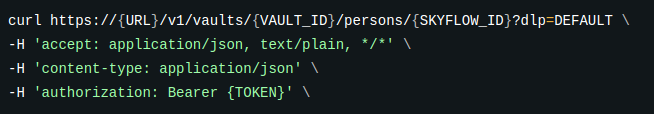
This data query aspect is interesting. Here the application will query the corresponding record, providing a ?dlp= parameter within the requesting URL. This parameter will indicate the format for how the data will be returned. Each vault and perhaps each table, has an associated DLP (data loss prevention) policy that controls how the returned data should be returned.
There seems to be 4 options: DEFAULT, TOKEN, REDACT and PLAIN.
DLP Queries
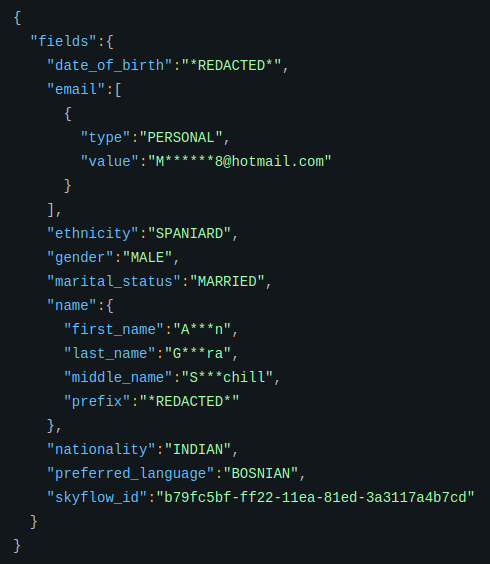
In their documented examples, this returns a payload can contains the date of birth as redacted and the email and name fields masked.
Role Based Access Control
The vault provides a range of role based access control permissions that can provide delegated administration capabilities. These seem to be broken down into: Admin roles (account admins, workspace admins) and Vault roles (creator, owner, editor, viewer). These essentially map into the control and data plane capabilities.
Encrypted Analytics
Another interesting feature the Skyflow vault provides, is that of encrypted analytics. This provides support to perform operations on data whilst it is still encrypted. This can clearly help reduce the data blast radius and prevent inferred information leaks against the stored data.
Tokenization
Tokenization is a design pattern that essentially allows for the swapping of a plain text data field with a token. That token is a cryptographically created value that doesn’t reveal anything regarding the original value. If the real value is needed, the token can be exchanged for the real value, based on DLP policy and permissions. Skyflow provides this functionality.
The latest release notes are available here.
