Google provides a range of cloud related identity and access management services. Let’s take a look […]
6 Minute Read.Let us start with some brief definitions to get us all on the same […]
Back in July, I wrote an article taking a brief look at venture capitalist funding patterns […]
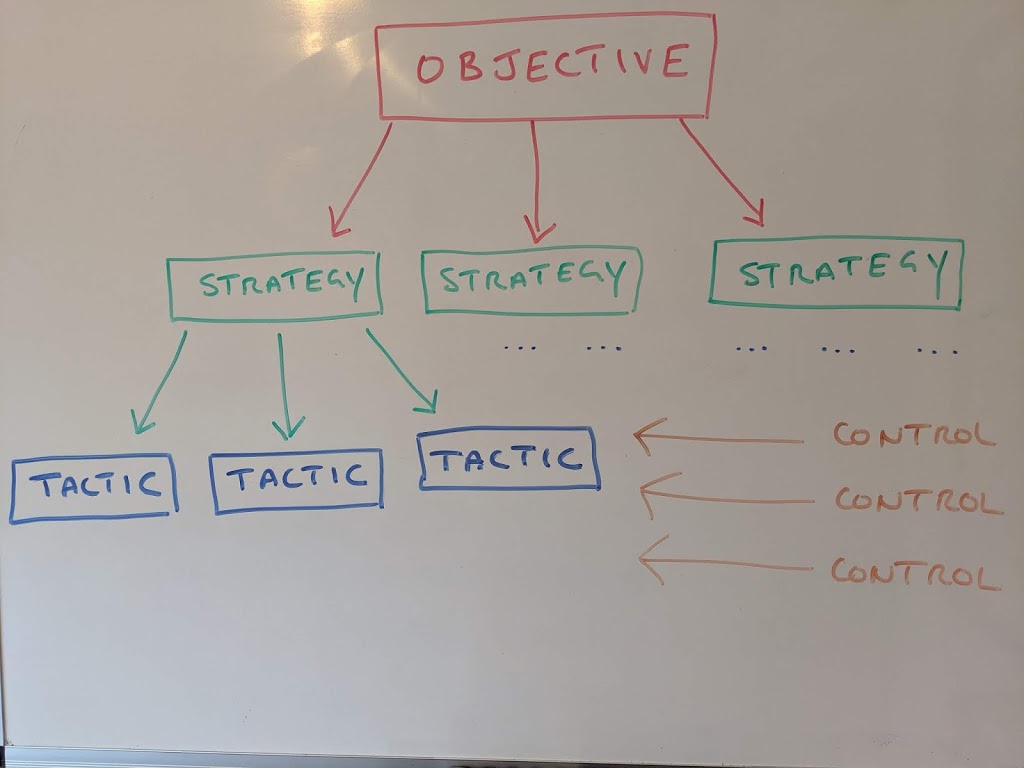
When it comes to cyber security design, there have been numerous ways of attempting to devise […]
I want to talk about the age old trade off between the simplicity of a website […]
As the first half of 2019 has been and gone, I’ve taken a quick look at […]
Today’s authentication requirements go way beyond hooking into a database or directory and challenging every user […]
Schools out for summer? Well not quite. Unless you’re living in the east coast of Australia, […]
Triple R’s of Security What are the “3 R’s of Security”? A quick Google on that […]
A Google search for “zero trust” returns ~ 195Million results. Pretty sure some are not necessarily […]